
Nowadays, Internet security is seriously compromised. Therefore, it is important to give you some new tips and suggestions to help you protect yourself. Of course, 100% protection does not exist. However, you can reduce the chances of malicious hackers harming you. A VPN network, or “private network” as some call it, is one of the ways to increase personal security online (you can check out VladTalks.tech for more VPN advantages). At a time when home-based work is becoming more common, we can’t help but wonder … How secure and reliable is communication with a remote device? And how resistant it is to “eavesdropping.”? The VPN network offers you good protection options.
What Is A VPN?

VPN is a private network used for communication within a public network. VPN data packets are transported over a public network (eg the Internet). This is achieved by using standard communication protocols. In simple vocabulary, we can look at a VPN as a kind of tunnel. It is created in an existing network. It means that a space enclosed by crypto walls is virtually created. There is network traffic inside that tunnel, while only certain people are allowed to access. For example employees of one company. Imagine a situation where you started working on a major project. You need the help of one of your colleagues currently in another country or even on another continent. Communication through the mails itself would be slow. On the other hand, you need to be on your local network for some apps that could work. The best way to do this is to configure VPN access to your network. So your colleague connects to your “private network” via VPN. This makes you feel like you’re on a local network and function as if you were in the same office.
How Does A VPN Work?
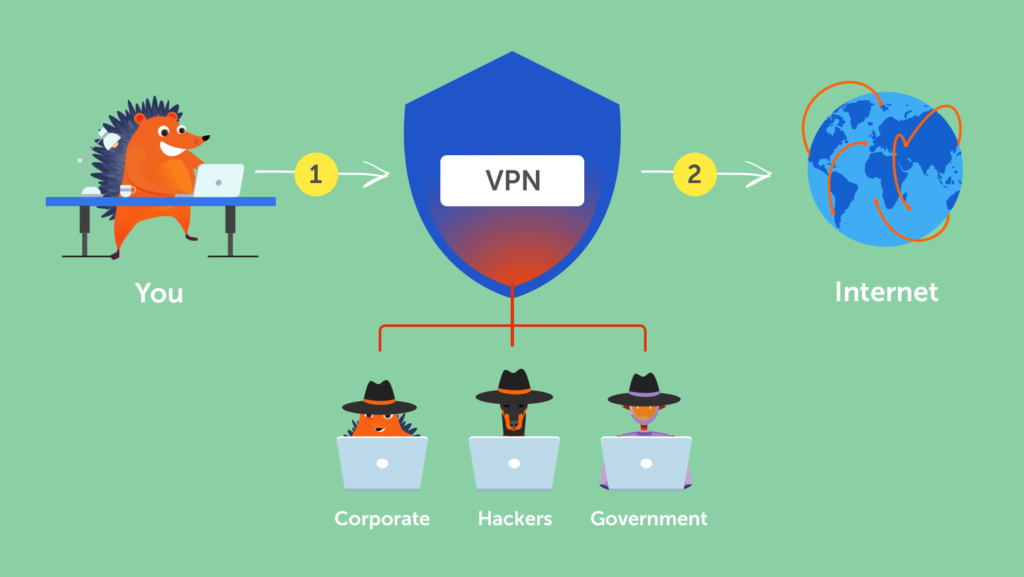
VPN allows users to exchange data via a point-to-point link between the client and the server. PPP emulation is obtained by encapsulating the header data. This header allows routing through the public network to destinations that are part of the private network. Data is encrypted. Packets that are intercepted within a public or shared network cannot be read. Unless you have the decryption key. According to Myvpnhound.com, public network infrastructure is irrelevant because the user logically sees only his private link.
What Is Tunneling?

The VPN principle introduces another term – tunneling. Tunneling is an integral part of VPN networks and represents the transmission of data packets. They are intended for a private network over a public network. Public network routers are not aware that they are transmitting packets belonging to the private network. They treat VPN packets as normal traffic. The tunnel represents the logical path of the packet. By that path, it is routed over the network. The encapsulated data is routed through a transport network from one end of the tunnel to the other. The information traveled by the tunnel is understandable only to those located at its source and destination. The start and end of the tunnel are in VPN networks. When the encapsulated packet arrives at its destination, decapsulation, and forwarding to the final destination take place. The whole process is called tunneling.
The concept of VPN is very common and quite extensive as a topic. VPN has also found its application in mobile technology.
















